There's an arms race happening right now. Every team, every product, every architecture review: agents, agents, agents. Pure Agent Smith energy: replicating across every program in sight, consuming everything he touches. The enthusiasm is real. But watching these agent chains get designed, I keep getting the same feeling Yogi Berra described perfectly: déjà vu all over again.
Jimmy Bogard's "Microservice Megadisasters" talk laid out how the industry charged into microservices with the best intentions and created distributed monoliths, chatty services, and coordination nightmares. We're doing it again. Different technology, same architectural sins.
So let's ask the uncomfortable question: are we losing the plot?
The Foundation: Vertical Slice & Autonomy
A vertically sliced agent owns its domain end-to-end: its tools, its context, its data. It doesn't share memory with other agents. It doesn't depend on a central orchestrator to function. It can act, decide, and complete its core task entirely within its own boundaries. That self-sufficiency is what makes real autonomy possible. Autonomy isn't something you grant through instruction. It's earned through design.
The spectrum runs from fully horizontal (shared everything, max coordination overhead) to hybrid via A2A (vertical slices with intentional, managed seams) to fully vertical (max autonomy, smallest blast radius). For most production systems, hybrid via A2A is the sweet spot: independent agents that communicate deliberately rather than constantly.
A simple gut check: if your agent routinely reaches outside its slice to complete its core task, the slice boundary is wrong.
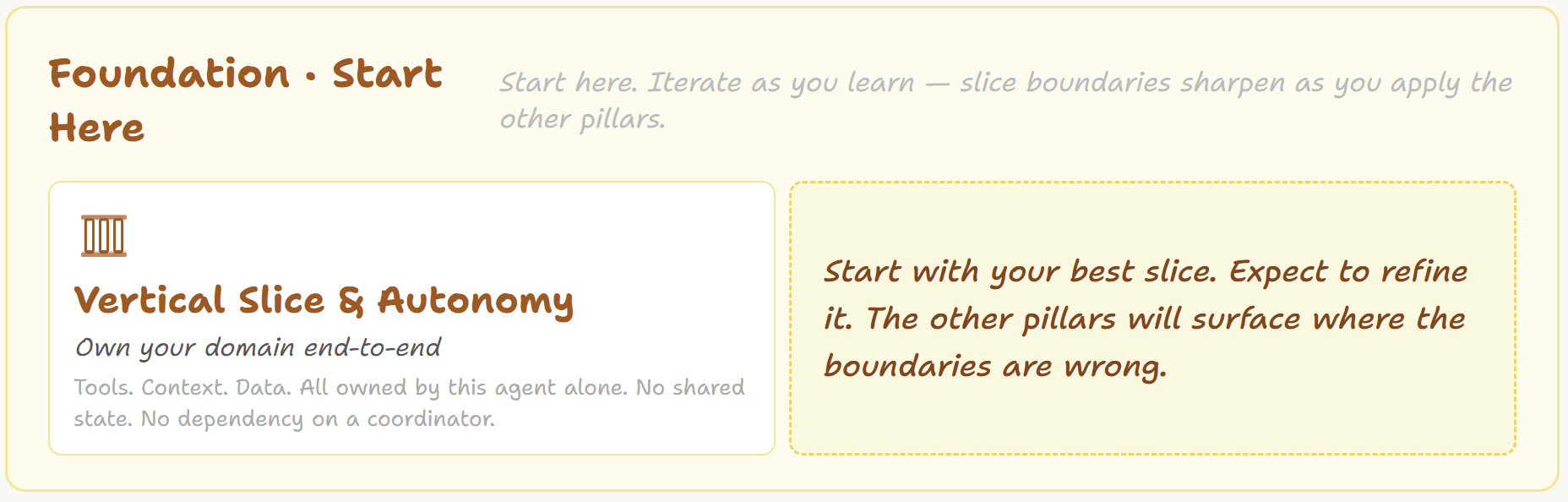
Define this before you do anything else. Everything downstream depends on getting the slice right.
Building It Right: The Cloud WAF Pillars, Adapted
Once you know what you're building, the question becomes how well you're building it. This is where the Well-Architected Framework, adapted for agentic systems, earns its keep.
Six pillars: Operational Excellence, Security, Reliability, Performance Efficiency, Cost Optimization, and Sustainability. Same intent as AWS WAF. Agent-specific guidance. A few of them hit differently here than in cloud land:
Reliability means designed for failure, not just designed for uptime. Every chain boundary is a fault domain. An agent that hands off half-finished work to the next agent in a chain, silently and confidently, is the failure mode that bites you in production. Fail-loud behavior, circuit breakers at the MCP layer, checkpoint/resume for multi-step runs.
Cost grows in unexpected places. Every token and every tool call has a cost. I've seen proposed agent solutions that cost more to run than the problem they're solving. Session budgets and loop detection from day one. Hard stop at 100%. Non-negotiable.
Security lives in code, not prompts. "Don't do X" in a system prompt is a suggestion. Trust tiers enforced at the MCP layer are a constraint. Credentials never enter the agent. Blast radius explicitly bounded.
Operational Excellence instruments all the others. SLOs, playbooks, postmortems. Every other pillar defines what good looks like. This one tells you if you still are.
And cutting across all of it: evals. Tool selection quality, argument accuracy, chain-of-thought faithfulness, hallucination rate. None of it is optional. Evals are the signal that tells you whether your agent is actually doing what you think it's doing.
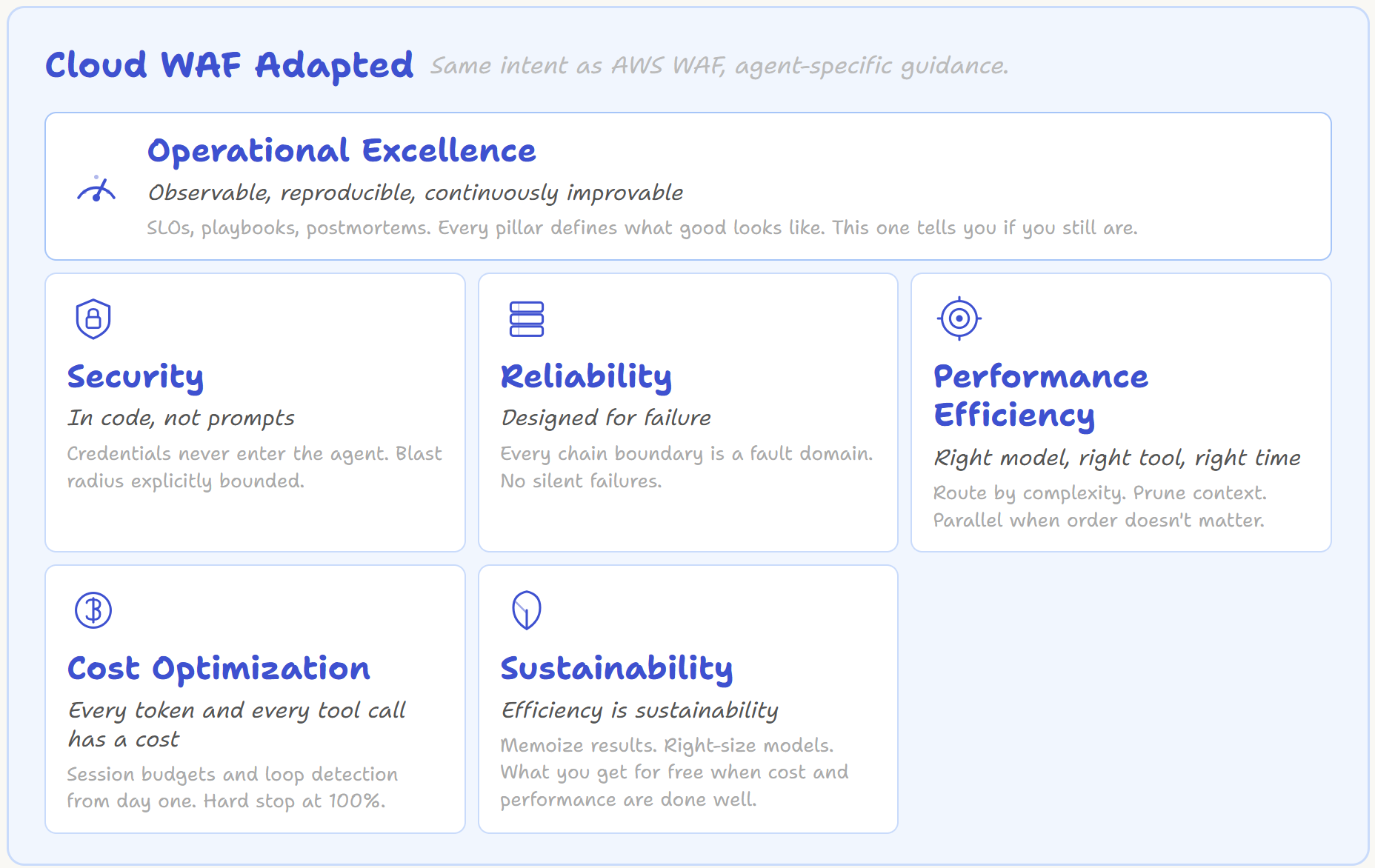
These six cover the build-and-run concerns. But agents introduce a class of risk that cloud architecture never had to contend with.
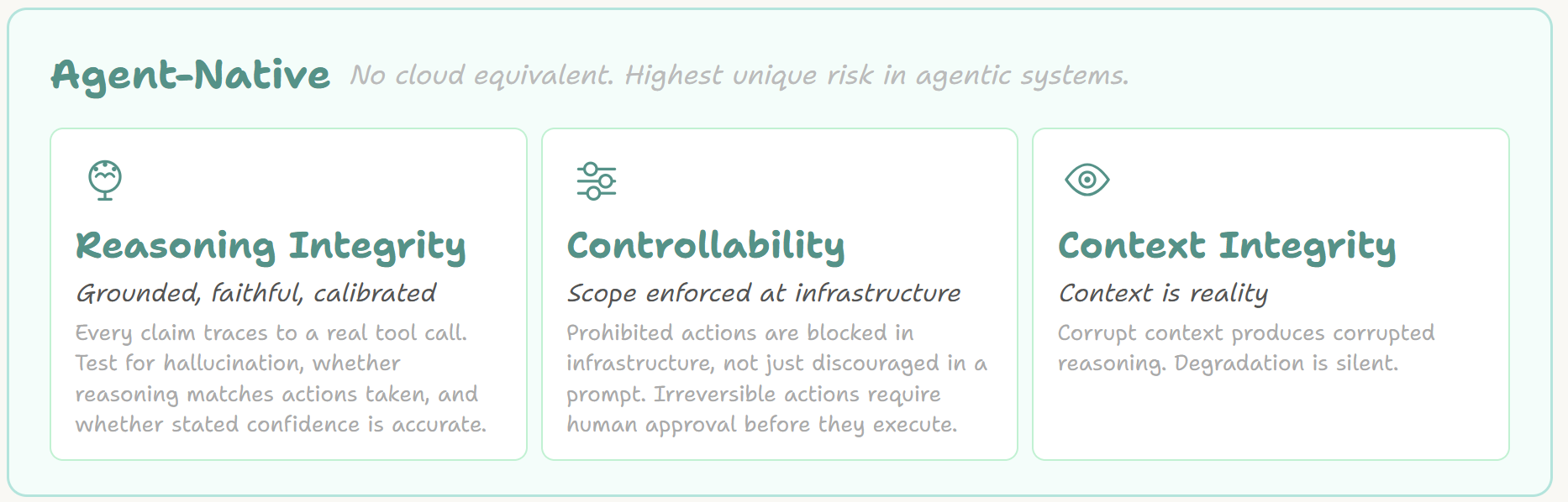
What's New: The Agent-Native Pillars
Cloud architecture doesn't have an equivalent for these. They're unique to systems where an LLM is doing the reasoning.
Reasoning Integrity is about the agent failing confidently and silently, which is the worst kind of failure. An agent can select the wrong tool, hallucinate an argument, go off-rails in its chain of thought, and still return a clean-looking result. Evals need to cover all of it. MCP should provide provenance metadata on every response so the agent can ground its claims.
Controllability means humans remain in control. Not through prompts that say "don't do X" (that's a suggestion), but through trust tiers enforced in code at the MCP layer. Any in-flight agent must be stoppable externally. The primitive is simple: pause, notify, then resume or abort.
Context Integrity might be the sneakiest one. Context is the agent's perception of reality. Stale context means corrupted reasoning. External content entering the agent through MCP needs to be sanitized. Long sessions need active lifecycle management. And critically: the agent needs to know what it doesn't know.
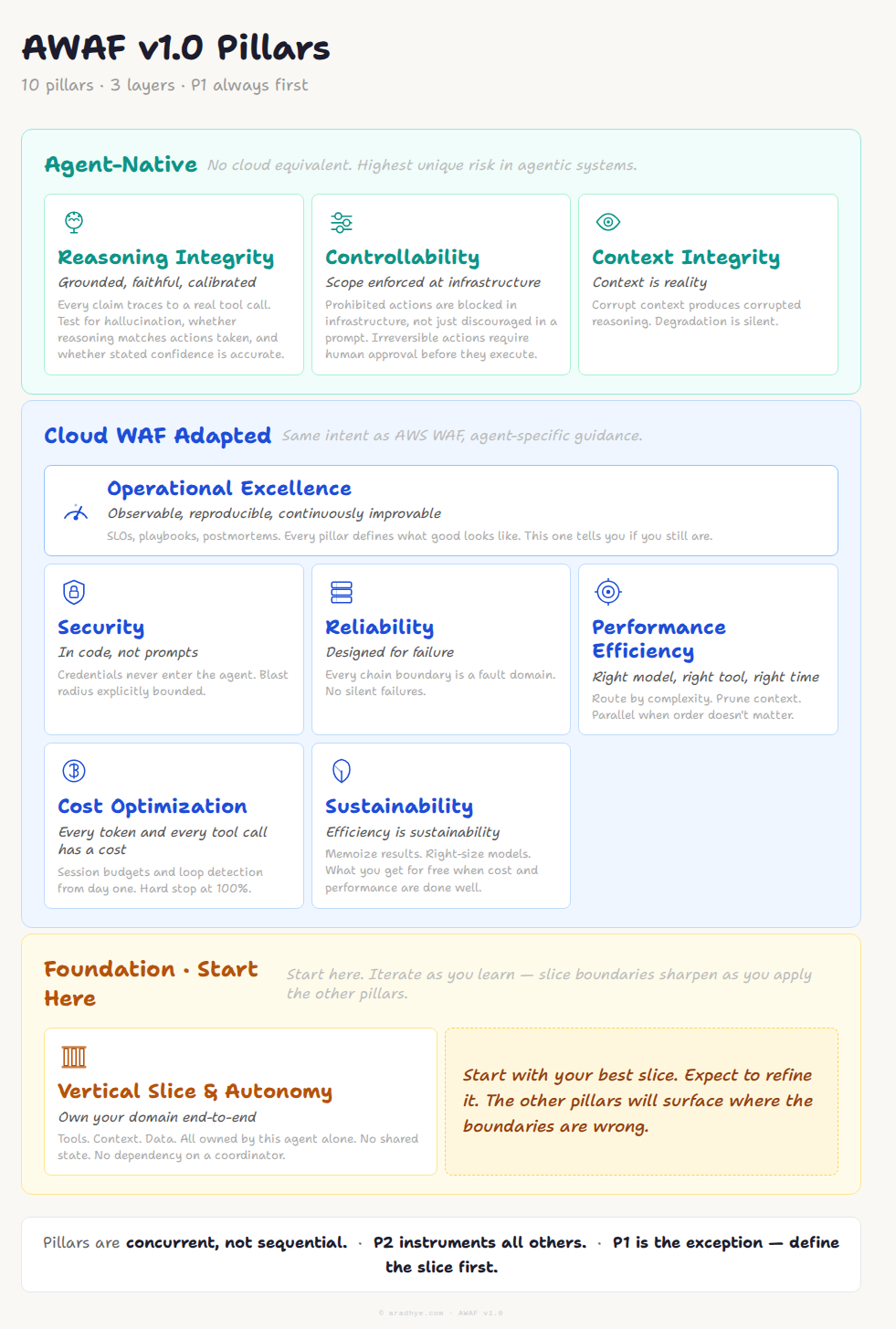
The Full Picture
Put it all together and you get AWAF v1.0, a production framework for AI agents at scale with MCP as first-class infrastructure.
The key principle worth repeating: these pillars are concurrent, not sequential. They're load-bearing walls, not a staircase. Operational excellence instruments all others. Security constrains Reliability. Reasoning Integrity depends on Context Integrity. The one exception is the foundation: the vertical slice. Define your vertical slice first, then apply the remaining nine.
The Bottom Line
Microservices weren't a bad idea. The bad ideas were how they were implemented at scale without the supporting discipline. Agentic AI isn't a bad idea either. But without architectural intentionality, we'll repeat the same expensive lessons.
AWAF gives us a frame of reference. Not a rigid checklist but a set of lenses to hold up against what we're building and ask: are we doing this right? Are we doing this cheaply? Are we doing this safely? Can we operate it in production without waking someone up at 3am?
Build the slice first. Then build it well.




Comments